You typed “about naolozut253” into Google because you saw the term somewhere — maybe a search result, a forwarded message, or a random link on social media. And now you’re staring at a wall of articles claiming it’s a digital fingerprint, a security protocol, an experimental code, and a mysterious online persona. All at the same time.
Here’s the problem. None of those articles agree with each other. One says it’s a cybersecurity tool. The next says it’s a username. A third says it’s an internal project code. They can’t all be right — and after investigating the top-ranking pages, the evidence points to a much simpler explanation.
Naolozut253 does not appear to be a real product, technology, standard, or recognized entity based on currently available public information. No government body, standards organization, or technology company has documented it in any widely accessible official source so far. The term exists online primarily because content farms published articles about it — and those articles are now ranking in search results, creating a self-reinforcing cycle of curiosity.
This guide breaks down what we actually know, what the ranking pages claim (and why their claims fall apart under scrutiny), and what you should do if you encounter this term — especially if you’re in Malaysia.
Table of Contents
Quick summary before we go deeper:
- Naolozut253 has no verified meaning — no official source has ever documented or defined it
- Content farms created articles about it — to capture curiosity-driven search traffic
- Top-ranking pages contradict each other — which strongly suggests the term was invented, not discovered
- The term itself isn’t dangerous — but links and files associated with it could carry risks
- Malaysian users can report suspicious content — through MCMC, MyCERT, and CyberSecurity Malaysia
What Is Naolozut253? (The Straight Answer)
Naolozut253 is an alphanumeric string that currently has no widely verified meaning, no official documentation, and no confirmed connection to any product, person, organization, or technology standard. It functions as what’s sometimes called a “fabricated keyword” — a term that gains search visibility not because it refers to something real, but because websites published content about it.
That’s it. No hidden technology. No secret code.
The reason you see so many articles about it is circular: blogs posted articles optimizing for the term, those articles got indexed, people saw the phrase when searching, searched for the phrase, and started the cycle all over again.. This pattern isn’t unique to Naolozut253. The same content-farm networks publish nearly identical articles about terms like Qushvolpix, B2K-ZOP3.2.03.5, and Kutop-CS.536b.
How Naolozut253 Became a Search Term
So if nobody invented it as a real technology — where did it come from?
The earliest articles about Naolozut253 that we can see in current search results appear in late 2025, published on guest-post blogs that accept submissions from anyone willing to write. By January 2026, multiple sites had published “explainer” articles targeting the exact phrase “about naolozut253.” The timing suggests a coordinated or templated content strategy rather than organic interest.
The Content Farm Publishing Pattern
Every site ranking for this term shares a pattern worth noticing:
- They all accept guest posts through “Write for Us” pages
- They publish articles about multiple fabricated terms — not just this one
- Authors use pseudonyms or generic names with no verifiable credentials
- Articles contain zero external citations or references to official sources
- Content hedges constantly with “appears to be,” “may function as,” and “could be”
Related Fabricated Terms From the Same Sites
This is where it gets interesting. The sites publishing about Naolozut253 also rank for articles about other invented alphanumeric terms. Technosidd.com, techyflavors.com, efindanything.com, and sbnewsroom.com all publish content about terms like Qushvolpix, B2K-ZOP3.2.03.5, Kutop-CS.536b, and qy-45y3-q8w32 — following the same vague “explainer” template each time.
When the same sites use the same format to explain dozens of different nonsensical terms? That’s a pattern. And it’s a pattern that should make you skeptical of any individual article’s claims.
What Top-Ranking Pages Claim — And Why They Contradict Each Other
Some of the strongest evidence that Naolozut253 is not a defined, real-world product or standard comes from comparing what the top-ranking pages actually say about it. If a term had a genuine definition, you’d expect some consistency. Instead, here’s what we found:
| Claim | Technosidd | Techyflavors | Efindanything | SBNewsroom |
|---|---|---|---|---|
| What is it? | Placeholder / coded reference | Digital fingerprint / security tool | Username / online handle | Digital tag / concept |
| Is it a product? | No | Describes it like one | No — it’s a person’s handle | No — it’s abstract |
| Security role? | Depends on context | Core MFA component | Not mentioned | Not mentioned |
| Who created it? | Unknown | Computer-generated | Created by a person | Unknown |
| Verified? | Not addressed | Presented as established fact | Presented as real | Not addressed |
Four pages. Four completely different definitions. One claims it’s a multi-factor authentication component (with zero citations to any security standard). Another says a specific person created it as a username. A third treats it as a vague concept.
If this were a real technology or product, at least two pages would reference the same source document, patent, company, or standard. None of them do — which strongly suggests there is no shared, verifiable source for their claims.
The Content Farm Network Behind Naolozut253
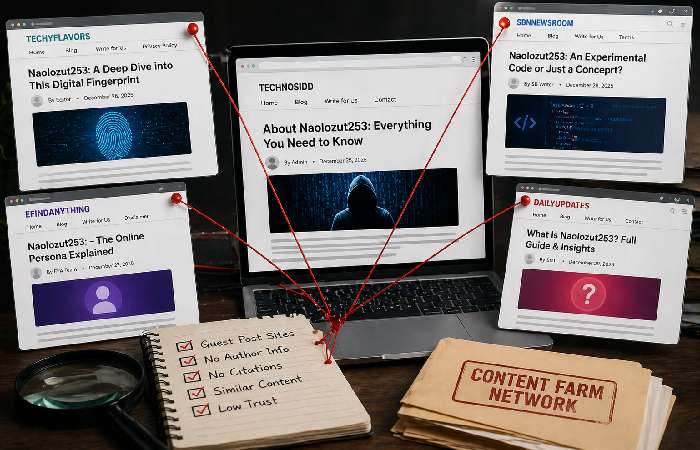
Who’s actually publishing these articles? Not cybersecurity researchers, technology journalists, or academics. The pages ranking for “about naolozut253” come from a specific category of website.
Site Profiles and Trust Signals
- Technosidd.com — Hosted on Google’s Blogger platform. No verifiable author. Publishes articles about fake Aadhar card services alongside tech explainers. Active “Write for Us” page.
- Techyflavors.com — Also Blogger-hosted. Author name is the site brand itself (“Techy Flavors”). The “About Us” link actually redirects to the Naolozut253 article — a broken site structure that suggests rushed or automated publishing.
- Efindanything.com — WordPress site with 1,229 pet articles, 458 health articles, and scattered tech content. Author “Bryan Davis” has no verifiable identity. The article uses 15 tag variations of “naolozut253” — pure keyword stuffing.
- SBNewsroom.com — The only site with a somewhat verifiable author (Piyasa Mukhopadhyay, MBA). But the article includes a section about how to rank for the keyword “about naolozut253” — literally teaching readers how to replicate the content-farm strategy within the article itself.
The “Write for Us” Guest-Post Pipeline
All four primary ranking sites actively solicit guest posts. This is the mechanism: someone writes a template article about a fabricated term, submits it to multiple guest-post sites, and each site publishes it (or a variation) to fill their content calendar. The writer gets a backlink. The site gets content. The reader gets nothing useful.
Is Naolozut253 a Person, Username, Code, or Product?
Since the ranking pages can’t agree, let’s assess each interpretation based on available evidence.
| Interpretation | Evidence For | Evidence Against | Likelihood |
|---|---|---|---|
| Real person | One page claims it’s a persona | No social profiles, no public records, no verifiable identity | Very Low |
| Username/alias | Follows username patterns (letters + numbers) | No matching accounts found on major platforms | Low |
| System code/identifier | Contains alphanumeric structure | No system, database, or protocol references it | Very Low |
| Security protocol | One page claims MFA connection | No RFC, no NIST entry, no CVE, no vendor documentation | Very Low |
| SEO-generated keyword | Published by known content farms, contradictory definitions, no official source | Could theoretically have a private, undocumented use | High |
The available public evidence strongly supports the final interpretation. Could Naolozut253 have some obscure, private meaning in someone’s internal system? Sure — any random string could. But the public-facing content about it is manufactured, contradictory, and unsourced.
Risks of Engaging With Unverified Online Terms
Naolozut253 itself is just a string of characters. It can’t hurt you. But the ecosystem around fabricated keywords does carry real risks worth understanding.
Phishing and Malware Vectors
Pages ranking for fabricated terms sometimes serve as vehicles for other things. A few risks that apply broadly to low-quality content sites:
- Malicious ads served alongside the article (programmatic ad networks don’t always vet advertisers)
- Download prompts for “tools” or “scanners” related to the term
- Links to other pages that request personal information
- Redirects to phishing pages disguised as login forms
This doesn’t mean every Naolozut253 article is dangerous. Most are just empty content. But the sites hosting them often lack the security infrastructure — HTTPS enforcement, ad quality controls, malware scanning — that reputable publishers maintain.
Misinformation and False Authority
The subtler risk is informational. When four articles confidently explain what Naolozut253 “is” — and all four say different things — readers who trust any single explanation end up misinformed. And if someone acts on that misinformation (say, by assuming Naolozut253 is a legitimate security feature and relaxing their actual security practices), the consequences are real.
What to Do If You Encounter Naolozut253
Uncertain that the term you‘ve stumbled across on the internet is the real deal? Here‘s a quick technique that may work on any Naalozut253 (or any other strange 8-Letter code).
Safety Checklist for Malaysian Users
- Avoid clicking links from untrustworthy sources. If Naolozut253 was received through a Whats App forward, SMS, or email consider it as any unknown link. Confirm the sent information!
- Search for the string in quotes. ” Naolozut253”. Searching in Google for“Naolozut253”, with quotes will result in only pages with that string, as is. If there are only blog articles and no sit official docs that gives you more information.
- Beforehand, review the publishing site. Does it have author credentials, citations, editorial policies, and a genuine About Us page? If a site only publishes 1,229 pet articles and one cybersecurity explainer, then you should trust its information less.
- Check URLs Before clicking on a link, Use Google Safe Browsing or VirusTotal to see if it is considered dangerous.
- Do not download anything. Files with extensions such as. Exe,. Apk,. Bat,. Scr or.zip from any unknown websites should be considered as suspicious.
-
Verify whether the standard is officially documented. Search for the term using official sources – IEEE Xplore, NIST, ISO or the applicable Malaysian regulatory agencies’ databases. If there is no reference to the standard, then the term is not a known standard.
If you want an even easier memory aid for dealing with any unknown identifier then you can remember what to do by using a four step safetymode that is, a way of thinking that’s always summarised as SCAN:
- S- Search the exact phrase in quotation marks: Simply place the string in quotation marks (e.g,“Naolozut253” and see what shows up. If only unsourced bloggers show up and no well-known, institutional sites exist then you should consider the statement unsubstantiated.
- C- First check whatever URL/file is associated: Hopefully, any no-risk facility will give you a chance to check the URL in a safe environment e.g. Google Safe Browsing, VirusTotal first and scan files on a secure workstation if you can.
- A- Think critically about the origin of the page/message. Who is it from? What is the domain? The content site? Are there author credentials? Is this a multi niche content farm? Where trust signs are absent be wary.
- N -No action (or report) if confused: if you check the site and can‘t verify legitimacy then don‘t take the requested action (click, login, pay, download). If it feels scammy then report it using the Malaysian channels given at the end of the instructions:
How to Report Suspicious Content in Malaysia
Malaysian users have several channels for reporting online threats:
- Malaysian Communications and Multimedia Commission (MCMC) — Reporting false or harmful content from internet
- MyCERT (Malaysia Computer Emergency Response Team) — Filing cyber incidents at mycert.org.my
- CyberSecurity Malaysia — Cybersecurity agency of the nation providing threat advisories and incident handling
- National Scam Response Centre (NSRC) —Incorrect! or for scam related reports call 997
How to Spot Fabricated Keywords (A Reusable Framework)

Naolozut253 won’t be the last fabricated term to show up in search results. This 5-point framework helps you evaluate any unfamiliar term you encounter:
- The Contradiction Test. Search the term and compare the top 3–5 results. If they can’t agree on a basic definition, the term probably doesn’t have one.
- The Source Test. Are they on specialized sites with credentialed authors, or are they produced by multi niche guest post farms? Look for ‘Write for Us’ pages they might not be indicative of poor content, but they are a sign to look for.
- The Citation Test. Does any article link to an official source — a standards body, a research paper, a company website, a government database? If every article references only itself or other blog posts, that’s a closed loop of unverified claims.
- The Pattern Test. Does the same site publish articles about other unfamiliar alphanumeric terms using the same template? If yes, you’re probably looking at a content-farm keyword strategy.
- The Official Source Test. Search for the term on Google Scholar, NIST, IEEE, or the relevant regulatory body for your country. If there’s nothing — not a single mention — you have your answer.
Why This Matters — Search Pollution and Digital Literacy
What’s happening with Naolozut253 isn’t an isolated incident. It reflects a broader pattern in how search engines can be gamed.
Content farms have discovered that fabricated terms — alphanumeric strings nobody has written about before — face zero competition.
The cost is borne by searchers. Someone who encounters Naolozut253 and genuinely wants to know if it’s safe doesn’t get a useful answer. They get speculation dressed up as expertise. That’s a problem — and it’s part of what Google’s helpful content system was designed to address.
For Malaysian users specifically, this matters because digital literacy gaps can be exploited. According to MCMC’s own communications, Malaysians are among the most active internet users in Southeast Asia. High engagement combined with unfamiliar terms creates exactly the conditions content farms exploit.
Common Mistakes When Researching Unknown Online Terms
Worth calling out a few things people get wrong:
- Trusting the first result. The first page Google shows you isn’t necessarily the most accurate — it’s the one that best matched its ranking signals. For a fabricated keyword with no authoritative source, those signals can favor content farms.
- Confusing confidence with credibility. An article that says “Naolozut253 is a core MFA component” sounds authoritative. But confidence without citations is just assertiveness — and assertiveness is easy to manufacture.
- Share before checking. Forward the message about a new term in an article on WhatsApp/Telegram does not increase its verifiability. It only increases the message‘s virality if you can‘t verify it.
- To ‘Just believe it is safe because it sounds harmless’’. The word is harmless but the links around it might not be. Never just take a topic at face value, check the source.
Who This Guide Is For / Who Should Skip It
This guide is useful for:
- Malaysian internet users who saw “Naolozut253” somewhere and want a straight answer
- Digital literacy educators looking for a real-world example of search-result manipulation
- SEO professionals studying how fabricated keywords create artificial SERPs
- Anyone who wants a practical framework for evaluating unfamiliar online terms
You can skip this if:
- You’re looking for an actual product page, download, or technical specification for Naolozut253 — it doesn’t exist
- You already understand how content farms operate and don’t need the educational sections
Final Verdict
Naolozut253 appears to function as a fabricated keyword in current search results. There’s no verified product behind it, no person, no protocol, no standard. The articles ranking for it were produced by content farms using guest-post networks, and they directly contradict each other on every fundamental question — what it is, who made it, and what it does.
Which doesn‘t mean it‘s dangerous. The word is by its definition ‘inert’. But the ‘content farm’ that surrounds it poor content, unsubstantiated face, possibly malicious advertising… is not. So do consider the safety checklist above. How about a five-criteria test that you can apply to any confusing term you come across? Also for Malaysian users, good dedicated reporting pathways in MCMC, MyCERT and the National Scam Response Centre.
The best response to a fabricated keyword isn’t panic. It’s verification.
Frequently Asked Questions About Naolozut253
Q: What does Naolozut253 mean?
Based on all publicly available information, Naolozut253 doesn’t have a verified meaning. It’s an alphanumeric string that content-farm blogs have written about — but no official source, standards body, or technology company has ever defined it. The top-ranking articles each assign it a different definition, which is itself strong evidence that no real definition exists.
Q: Is Naolozut253 real or fake?
It depends what you mean by “real”. The string is real you can type it, you can search for it, you can find articles about it. As a product, a technology, a security standard or protocol, there‘s no verifiable evidence for any of it.
Q: Is Naolozut253 a person?
No confirmed public identity matches this term. One article frames it as a “digital enigma” persona, but provides no verifiable social profiles, public records, or contact information. The most likely explanation is that it’s a randomly generated or deliberately constructed string — not a person’s name.
Q: Is it safe to click on articles about Naolozut253?
The articles are mostly just empty content ones unlikely to cause any harm directly. However, the website storing them may contain poor quality advertising, snoop on you, or link to other pages, which may request information about you. Use an ad blocker, avoid downloading anything and do not enter any details of yourself.
Q: Why is Naolozut253 trending online?
It is getting popular because content farms published articles about it, Google indexed those articles, curious users searched for that and content farms published even more articles to get that traffic. It‘s a loop that‘s artificial rather than a real thing that people are interested in.
Q: Where can I find official information about Naolozut253?
You can‘t simply it isn‘t seems to be anything official on this. When I search the likes of IEEE Xplore, NIST, ISO standards and Google‘s Scholar or even the Malaysian regulator sites (MCMC, MyCERT) I can find nothing on this term.
Q: How is Naolozut253 connected to cybersecurity?
Another ranking article suggests that it is related to multi-factor authentication however it is mysteriously lacking of any such reference, RFC, vendor documentation or protocol specification. There is no evidence, there is no authority, it has the appearance of fake content.
Q: How can Malaysian users report suspicious online content?
Channels that provide messages. There are 3 main channels are MCMC (mcmc.gov.my) for cung information, MyCERT (mycert.org.my) for cybersecurity incidents and National Scam Response Centre (call 997) for scam-related reporting.
Q: Are all articles about Naolozut253 untrustworthy?
Not necessarily “all” — but every article currently ranking for this term was published on a guest-post blog, uses hedging language, provides zero citations, and contradicts at least one other ranking article. That pattern warrants skepticism.
Q: How do I know if a keyword is fabricated?
Use the 5-point method outlined here: cross check for cross-site contradictions, assess the sites of publication, cross check for citations to official sources, cross check to see if the same sites publish similar articles about different unfamiliar terms, and cross check the individual term on official databases. If doesn‘t pass all five, then assume it‘s fake.
Disclosure: This content was written in the context of educational awareness and online safety purposes. Information in this guide is based on currently available public sources, including search result analysis, general cybersecurity references, consumer protection resources, and publicly accessible web records related to Naolozut253. We are not affiliated with Naolozut253 or any website mentioned unless explicitly stated. This article aims to assist the user in recognizing the use of deceptive search queries, spotting the trends of content farms, and take more caution to the internet. As both these search logs and the online data are ever-changing, the reader is advised to always check further documentation with an authoritative agent.

